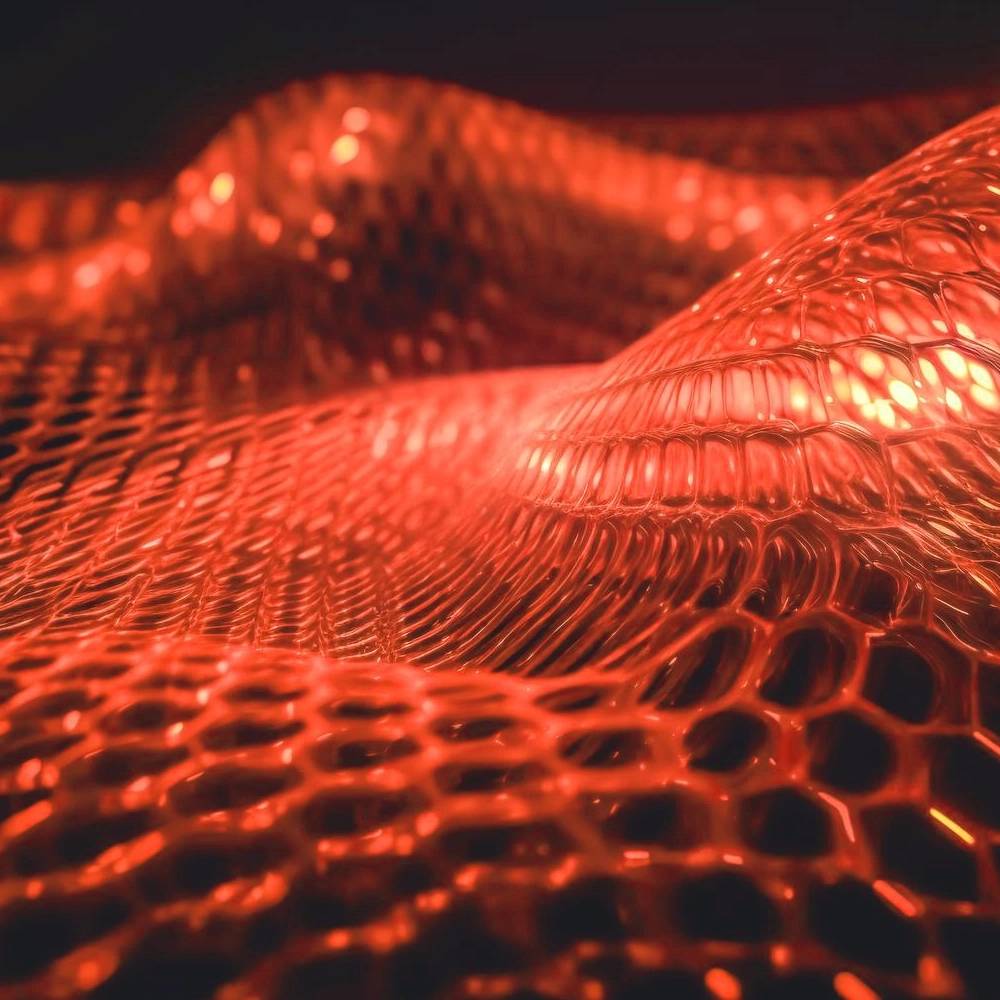
Artificial Intelligence Penetration Testing
Scope AI security assessments, provide third-party AI/pen test engagements, provide testing results, Translate technical findings into clear risk statements and remediation guidance for security leadership deal stakeholders, Track AI security risks through remediation and integration milestones.

AI Penetration Testing Categories
Perform adversarial security testing of AI and GenAI systems, including LLM-powered applications, Agentic workflows and AI automations, RAG pipelines, plugins, and tool integrations.
Execute AI-specific attack scenarios such as prompt injection, data leakage, jailbreaks, tool/function abuse, insecure output handling, and authorization bypass.


Artificial Intelligence Pen Test Methodology
Develop and maintain repeatable AI testing methodologies and tooling that can be reused across acquisitions and internal products.
Validate remediation and perform regression testing on AI-related security findings.

Managed Security Services
24/7 monitoring with advanced SIEM systems for real-time detection.

ICS IT/OT Security Architecture
Protecting critical assets across renewable energy, manufacturing, oil and gas and electricity industries

Security Audit and Assessment Readiness
PCI, NERC-CIP, SOC2, ITSG33
Why Choose Us
Complete Cyber Defense Against Modern Attacks
Stay protected with a fully integrated defense strategy built for today’s complex cyber landscape. From ransomware to phishing and zero-day exploits, we provide comprehensive protection across networks, endpoints, and cloud environments.

Need 24/7 Protection From Cyber Attacks?